
Securing and protecting our nation’s cyber networks is a key priority for the Science and Technology Directorate (S&T).
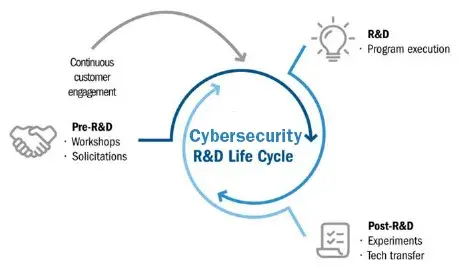
S&T conducts and supports research, development, test and evaluation (RDT&E), and the transition of advanced cybersecurity and information assurance technologies to secure the nation’s current and future cyber and critical infrastructures. These solutions include user identity and data privacy technologies, end-system security, law enforcement forensic capabilities, secure protocols, and software assurance.
S&T supports both internal DHS Components (e.g., Cybersecurity and Infrastructure Security Agency or CISA) and external federal agencies (e.g., FBI) by developing cutting-edge technologies in areas such as:
- Cyber Data Analytics
- Machine Learning (ML)
- Artificial Intelligence (AI)
- Automotive Cybersecurity
- Software Assurance
- Mobility
DHS S&T works to strengthen the nation’s cybersecurity with the latest and best innovations by partnering with national labs and stakeholders from the private sector to develop advanced critical infrastructure and cyber capabilities. Private sector stakeholders include small businesses, international partners, law enforcement and other first responders, industry, and academic groups.
There are several R&D efforts under way to develop new capabilities, which include:
- CISA Advanced Analytics Platform for Machine Learning (CAP-M): A joint effort with CISA to develop an R&D environment for advanced analytics.
- Cyber Analytics and Platform Capabilities (CAP-C): An effort supporting CISA with R&D to advance malware analysis through automation and to develop technology for active defense techniques.
- Software Assurance, Maturity, and Composition (SAMC): An effort to develop software assurance and ML models to increase the security and integrity of the software supply chain.
Visit S&T Impact: Cybersecurity to watch video and learn more about how we improve cybersecurity capabilities through strategic research and development.
- Blog: Stay Safe Online
- Technologically Speaking Podcast: Keeping Criminals Up at Night
- Technologically Speaking Podcast: Pain That Hurts and Pain That Alters
- Technologically Speaking Podcast: It’s Going to Be World Changing
- Feature Article: Testing Environments Help S&T and CISA Secure Transportation Infrastructure
- Blog: Ensuring Our Workforce Is Cyber Ready
- Blog: Taking Ownership of Our Cybersecurity
- Blog: New Funding Opportunities Aim to Strengthen Cyber Infrastructure
- News Release: DHS and Israeli Partners Announce Collaboration on Cybersecurity
- Feature Article: S&T Report Peers into the Future of 5G & 6G
- Blog: Training a Resilient Workforce to Secure our Critical Infrastructure
- Feature Article: A Secure Environment to Create the Future of Cybersecurity Solutions
- News Release: DHS S&T Releases Artificial Intelligence & Machine Learning Strategic Plan
- News Release: DHS S&T Expands Pilot of Cybersecurity Tech for Emergency Communications Centers
Learn more about us and discover how your organization can partner with S&T to make the homeland more secure.
