 Bridging the gap between research and the marketplace requires a transition process specifically designed to accelerate technology maturity and create partnerships with the private sector and the venture community. The Department of Homeland Security (DHS) Science and Technology Directorate’s (S&T) created the Transition to Practice (TTP) program to address this need. Through TTP, DHS S&T is leading the successful transition of federally funded cybersecurity technologies into broader use through commercialization and adoption by end-users. The TTP program has three main goals.
Bridging the gap between research and the marketplace requires a transition process specifically designed to accelerate technology maturity and create partnerships with the private sector and the venture community. The Department of Homeland Security (DHS) Science and Technology Directorate’s (S&T) created the Transition to Practice (TTP) program to address this need. Through TTP, DHS S&T is leading the successful transition of federally funded cybersecurity technologies into broader use through commercialization and adoption by end-users. The TTP program has three main goals.
- Identify promising technologies that address an existing or imminent cybersecurity need that impacts national security.
- Increase utilization through partnerships, product development efforts and commercialization.
- Improve the long-term ability of federal government research organizations to transition technology more efficiently.
Watch the S&T Cybersecurity Transition to Practice Video
As of 12/2016
Motivation
Technology transition remains a difficult endeavor with many challenges. Only a small fraction of the research performed in federal laboratories reaches the marketplace where it can have an impact. This problem, known as “the Valley of Death,” is often a result of lack of partnerships between the government and the private sector, nonexistent funding and other resources to mature the technology, and inefficient processes for transitioning technology out of the laboratory environment. Successfully transitioning cybersecurity technology from research to operational use is identified as a critical area in the 2016 Federal Cybersecurity R&D Strategic Plan.
Approach
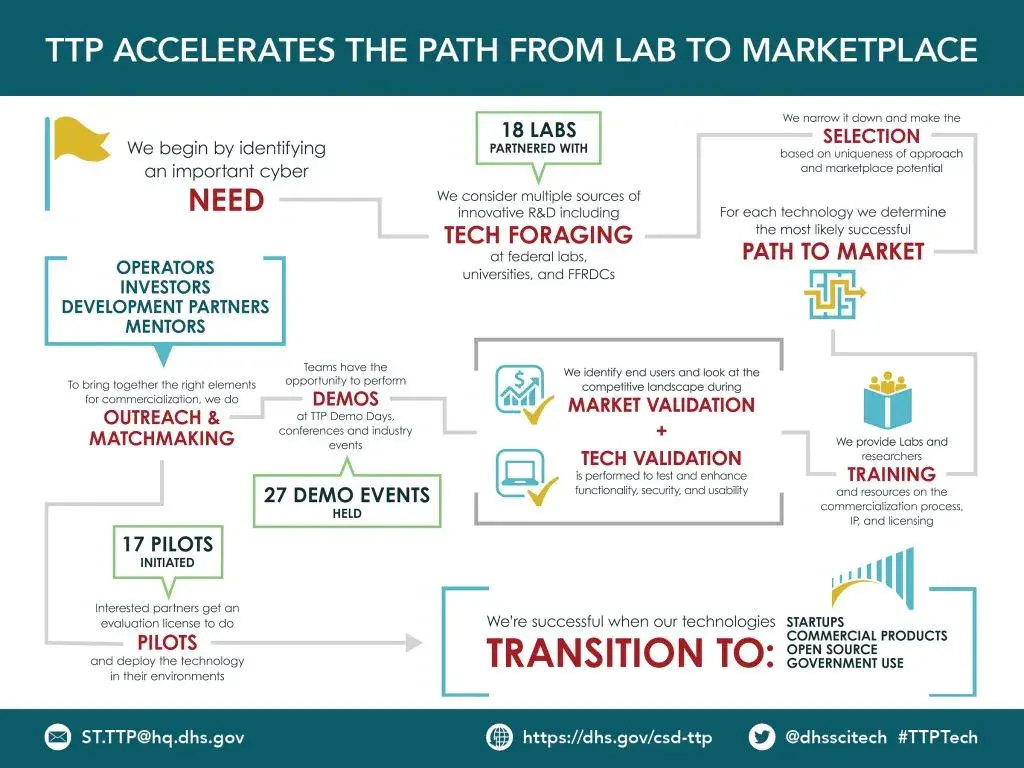
The TTP program conducts technology foraging to find the most promising cybersecurity projects across the federal government that demonstrate potential for commercialization. Selected technologies go through a structured process designed to accelerate the path from lab to market that includes training, market validation, testing and evaluation, pilot deployment, and outreach. TTP technologies are introduced to potential partners, investors and integrators and showcased at a national series of technology demonstration days. TTP supports multiple paths to transition, including licensing, startup creation, open source and government use.
Performers
The TTP program identifies promising cybersecurity technologies from several sources of federally funded R&D, including:
- Department of Energy National Labs
- Department of Defense-Affiliated Labs
- Federally Funded Research and Development Centers (FFRDC)
- University-Affiliated Research Centers (UARC)
- Universities receiving federal grants
Accomplishments/Impact
Since its inception in 2012, the TTP program has successfully transitioned more than a dozen federally funded cybersecurity technologies and helped create several cybersecurity startups to include the following:
AMICO (University of Georgia, NSF grantee): Available as open source
DigitalAnts (PNNL): Licensed by IP Group; product in development
Flower (PNNL): Licensed to zSofTech Solutions; product is part of cybersecurity offering
Hone (PNNL): Available as open source
Hyperion (ORNL): Licensed to Lenvio Inc; product in use by government and large corporations
Keylime (MIT Lincoln Lab): Available as open source
LOCKMA (MIT Lincoln Lab): Licensed to several companies for use in government solutions
MLSTONES (PNNL): Licensed by IP Group; product in development
NeMS (LLNL): Licensed to Cambridge Global; in development
PACRAT (PNNL): Licensed to Rhino Corp; adding capability to existing product
PathScan (LANL): Licensed by Ernst & Young; product is part of cybersecurity offering
PCapDB (SNL): Available as open source
PEACE (WPI, NSF grantee): Available commercially from ContexSure Networks LLC, a cyber security startup
REnigma (JHU APL): Available commercially from Deterministic Security, a cyber security start up
SCOT (SNL): Available as open source
SerialTap (PNNL): Licensed by IP Group; product in development
Quantum Security (LANL): Licensed to Whitewood Encryption Systems; available commercially
ZeroPoint (University of North Carolina, NSF grantee): Available commercially from ZeroPoint Dynamics, a network security start up
Resources
For the latest information about S&T Cybersecurity, visit the S&T Cybersecurity News, Publications, Videos and Events pages.
